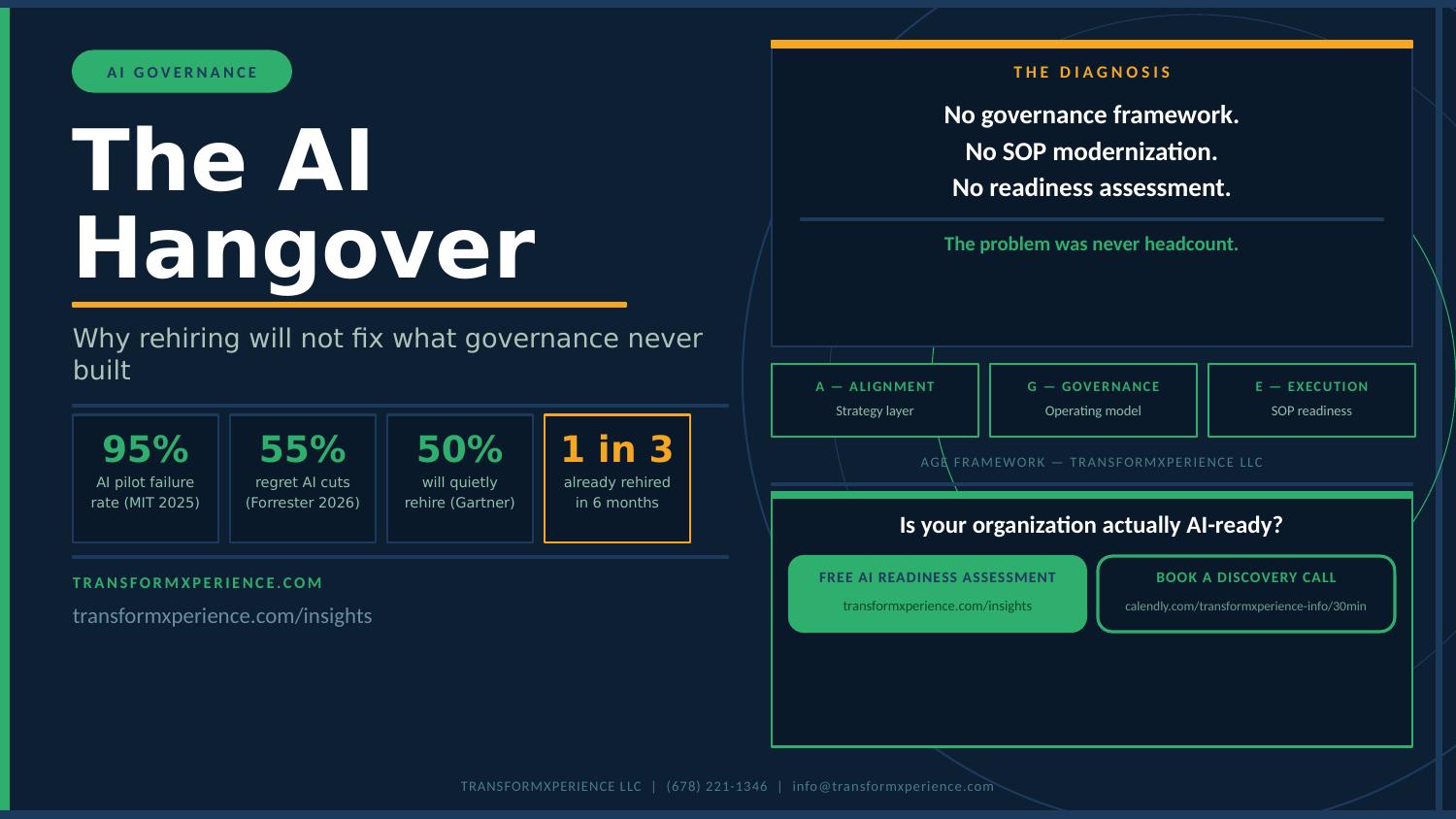
Introduction
For too long, cybersecurity has been viewed primarily as a defensive shield—a necessary cost center, a complex compliance burden, or worse, a reactive response to the latest breach. This traditional mindset overlooks a fundamental truth in today’s digital economy: cybersecurity is no longer just about protection; it’s a powerful strategic enabler that can unlock innovation, build trust, and drive a competitive advantage.
For CIOs and IT leaders, shifting this perception within the organization is crucial. It’s about transforming cybersecurity from a departmental chore into a core pillar of your enterprise’s growth strategy, actively protecting and enhancing your most valuable digital assets.
The threat landscape demands immediate action. Ransomware attacks increased by 41% in 2024, costing organizations an average of $4.45 million per breach, while supply chain attacks now target 62% of organizations. With AI-powered threats emerging as new attack vectors and cyber incidents becoming the leading cause of business disruption, the window for strategic cybersecurity transformation is rapidly closing.
The Current Threat Reality: Why Strategic Security Can’t Wait
Today’s cybersecurity challenges require more than traditional defensive approaches:
- Evolving Attack Sophistication: Cybercriminals now leverage AI and machine learning to create more sophisticated, targeted attacks that traditional security measures struggle to detect.
- Expanding Attack Surface: Cloud adoption, remote work, and IoT proliferation have dramatically expanded the attack surface, with 68% of business leaders feeling their cybersecurity risks are increasing.
- Regulatory Pressure Intensifying: New data privacy regulations and compliance requirements emerge quarterly, with non-compliance fines reaching up to 4% of global revenue.
- Business Continuity at Risk: The average cost of downtime from cyber incidents now exceeds $5,600 per minute, with some organizations facing weeks of operational disruption.
The Paradigm Shift: From Cost Center to Growth Catalyst
Consider the modern enterprise: every transaction, every customer interaction, every operational process is increasingly digital. In this reality, robust cybersecurity doesn’t just prevent loss; it actively facilitates business by:
- Fostering Trust & Reputation: Customers, partners, and investors are more likely to engage with an organization they trust to protect their data. A strong security posture builds an invaluable reputation. Organizations with mature cybersecurity report 73% higher customer trust scores and 50% faster digital transformation adoption.
- Enabling Innovation & Agility: When security is built-in (“security by design”), rather than bolted on, it empowers teams to innovate faster, deploy new digital products, and embrace emerging technologies (such as cloud and AI) with confidence, knowing that risks are managed. Security by design reduces development costs by 30% and accelerates time-to-market by 40%.
- Supporting Market Expansion: Meeting stringent global and industry-specific compliance requirements (e.g., GDPR, HIPAA, CCPA) isn’t just about avoiding fines; it opens doors to new markets and partnerships that demand a high level of data protection. Compliance-ready organizations capture 25% more international business opportunities.
- Ensuring Business Continuity: A resilient cybersecurity framework minimizes downtime from attacks, ensuring that critical operations remain functional, even under duress. Organizations with mature security programs experience 85% less downtime and recover 3x faster from incidents.
- Protecting Intellectual Property: Your digital assets include valuable trade secrets, R&D, and proprietary data. Strategic cybersecurity safeguards these vital components of your competitive edge. IP protection through cybersecurity has saved organizations an average of $2.3M in competitive advantage annually.
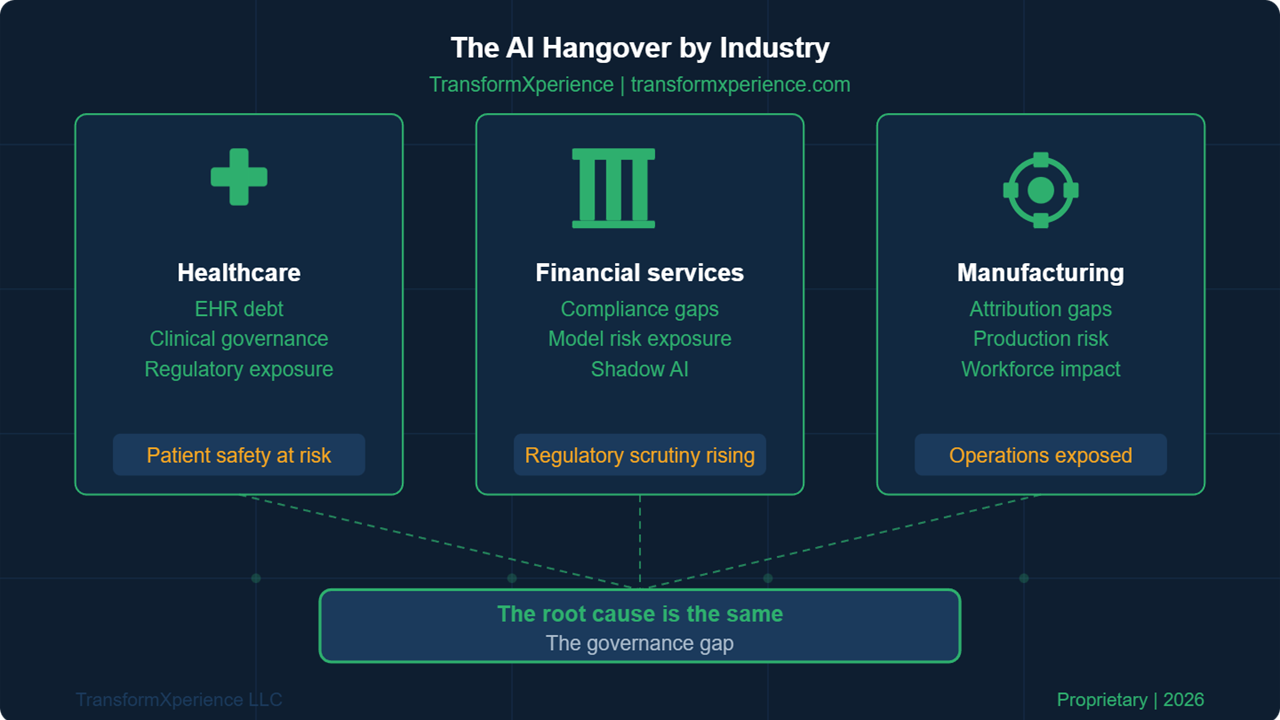
Industry Success Stories: Security as Business Enabler
Leading organizations across industries are realizing significant returns from strategic cybersecurity investments:
Healthcare Sector:
- Major health system achieved HIPAA compliance excellence, enabling new patient data services that generated $15M in additional revenue while reducing compliance costs by 45%
Financial Services:
- Regional bank’s Zero Trust implementation reduced fraud losses by 65% and accelerated digital banking adoption by 55%, resulting in $8M annual savings
Manufacturing:
- Global manufacturer’s OT security program protected $2.3B in intellectual property while enabling secure IoT integration that improved operational efficiency by 28%
Retail Industry:
- E-commerce leader’s comprehensive security posture increased customer trust by 73%, directly correlating to a 23% improvement in customer lifetime value
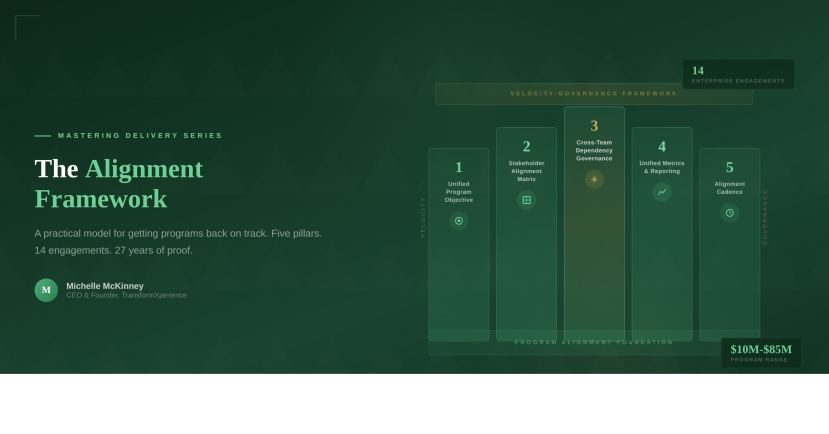
Key Pillars: Embracing Cybersecurity as a Strategic Enabler
To achieve this strategic shift, organizations must focus on these interconnected pillars:
1. Integrated Security Architecture
Beyond Silos: Move away from disparate security tools and point solutions. Adopt a unified, integrated security architecture that provides centralized visibility, automates responses, and correlates threat intelligence across your entire ecosystem (endpoints, networks, cloud, applications).
Zero Trust Principles: Implement Zero Trust, where no user or device is inherently trusted, regardless of their location. This granular approach significantly reduces the attack surface. Organizations implementing Zero Trust see a 50% reduction in breach costs and a 60% improvement in threat detection times.
2. Proactive Threat Intelligence & Risk Management
Anticipate, Don’t Just React: Leverage advanced threat intelligence feeds and security analytics powered by AI/ML to anticipate potential attacks and vulnerabilities specific to your industry and digital footprint. AI-powered threat detection improves response times by 65% and reduces false positives by 70%.
Risk-Based Prioritization: Focus security investments where the risk and potential business impact are highest. Develop robust incident response plans that are regularly tested and updated. Risk-based security approaches deliver 3x higher ROI than generic security implementations.
3. Compliance as a Competitive Advantage
Beyond the Checklist: View compliance with regulations (such as GDPR, CCPA, HIPAA, and PCI DSS) not as a burden, but as a framework for building best-in-class data protection and privacy practices.
Market Differentiation: Being demonstrably compliant and secure can be a key differentiator when attracting and retaining customers, especially in sensitive industries. This also reduces your exposure to regulatory fines (e.g., Data Loss Prevention mechanisms). Compliance-excellence organizations win 40% more competitive deals and command 15% price premiums.
4. Security by Design & Automation
Bake It In, Don’t Bolt It On: Integrate security considerations into the earliest stages of software development (DevSecOps), infrastructure planning, and new digital product launches. Security should be a foundational requirement, not an afterthought.
Automate Where Possible: Automate security tasks, such as vulnerability scanning, patch management, and intrusion detection, to reduce human error and improve response times. Security automation reduces operational costs by 35% and improves incident response speed by 80%.
5. The Human Element & Culture of Security
Your Strongest Firewall: Recognize that your employees are both your greatest vulnerability and your most vigorous defense. Implement continuous security awareness training that makes cybersecurity relevant and actionable for everyone. Organizations with a strong security culture experience 70% fewer successful social engineering attacks.
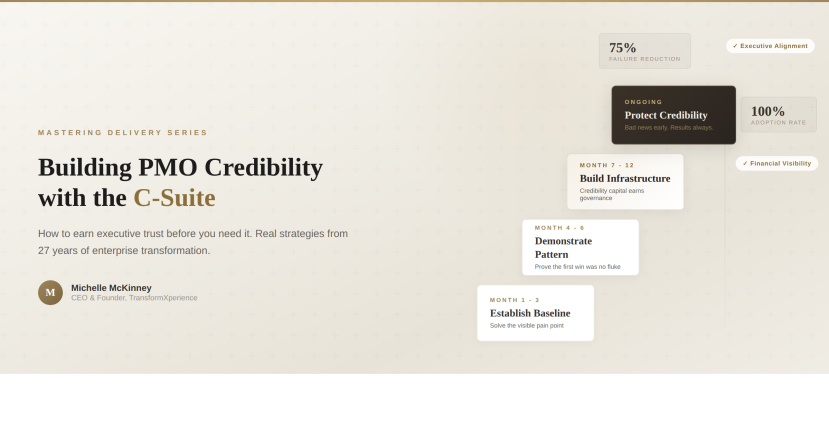
Top-Down Commitment: A strong security culture begins with leadership. The C-suite must champion cybersecurity as a core business value, not just an IT responsibility.
Cybersecurity Maturity Assessment: Evaluate Your Strategic Readiness
Before embarking on your cybersecurity transformation, assess your current maturity across these critical dimensions:
Technology Infrastructure (Foundation Level)
- Endpoint, network, and cloud security integration
- AI/ML-powered threat detection capabilities
- Zero Trust architecture implementation
Processes & Governance (Management Level)
- Security policies and incident response procedures
- Compliance framework alignment
- Risk management and business continuity planning
People & Culture (Organizational Level)
- Security awareness and training programs
- Executive sponsorship and governance
- Internal security expertise and capabilities
Threat Intelligence (Advanced Level)
- Proactive monitoring and threat hunting
- Industry-specific threat analysis
- Automated response and remediation capabilities
Organizations scoring high across all dimensions achieve a 4x faster security ROI and experience 60% fewer security incidents than those with foundational gaps.
Investment Benchmarks: Security as Strategic Priority
Leading organizations allocate cybersecurity resources strategically:
- Budget Allocation: Best-in-class organizations invest 3-5% of their IT budget in cybersecurity, compared to 1-2% for lagging organizations
- ROI Expectations: Comprehensive security programs typically deliver 300-400% ROI within 18-24 months
- Transformation Timeline: Strategic security transformation typically requires 12-18 months for full implementation and maturity
TransformXperience’s Role: Elevating Your Cybersecurity Posture
At TransformXperience, we partner with CIOs and IT leadership to transform cybersecurity from a reactive cost center into a proactive strategic enabler:
- Strategic Security Roadmapping: We help you define a cybersecurity strategy that aligns directly with your business objectives, risk appetite, and growth ambitions. Our strategic assessments typically identify 5-7 high-impact security improvements with a projected ROI of 250-350%.
- Integrated Risk Management & Governance: Our expertise in robust program governance, data integrity, and compliance enables you to navigate complex regulations and manage risks effectively, including the development of comprehensive Data Loss Prevention (DLP) strategies using advanced platforms like Azure Security Center and Sentinel.
- Solution Implementation & Optimization: We guide the implementation of advanced security solutions, from Zero Trust architecture and identity and access management to cloud security frameworks powered by AI/ML threat detection.
- Resilience & Business Continuity: We help build and test your incident response plans, ensuring your business can quickly recover from disruptions with minimal impact to operations and revenue.
- Building Internal Capability: We work to transfer knowledge and enhance the proficiency of your internal teams in modern cybersecurity practices, creating sustainable security excellence.
Take Action: Begin Your Security Transformation
Ready to transform cybersecurity from shield to strategic enabler? Here’s how to start:
Security Maturity Assessment: Request our complimentary Cybersecurity Maturity Assessment—a comprehensive evaluation that identifies your highest-impact security improvements and quantifies potential ROI across your organization.
Strategic Planning: Schedule an executive security briefing with our cybersecurity experts to develop a customized roadmap that aligns security investments with your business objectives and risk tolerance.
Pilot Implementation: Launch with a focused security initiative that demonstrates business value while building organizational confidence and security expertise.
Conclusion
The digital future is here, and with it, an evolving landscape of threats and opportunities. By embracing cybersecurity as a strategic enabler, your organization can move beyond merely reacting to risks. You can foster greater trust, accelerate innovation, expand into new markets, and build unparalleled resilience, securing not just your digital assets but your entire future growth trajectory.
With cyber threats intensifying and security becoming a competitive differentiator rather than just a protective measure, organizations that act decisively on strategic cybersecurity transformation will capture market opportunities while those that delay risk falling victim to increasingly sophisticated attacks.
Let TransformXperience help you transform your cybersecurity from a shield into a powerful engine for strategic advantage.
Ready to elevate your cybersecurity from protection to strategic enablement? Schedule a consultation with TransformXperience today to begin your cybersecurity maturity assessment and unlock the competitive advantages of strategic security.